<Update 2018-02-06>Updated with snippet to list out GUIDs for app roles that can be assigned.</Update>
In this post I will show how to automate the creation of an Azure AD Application and assign OAuth permissions to that application. The latter part is tricky as there is not currently a PowerShell commandlet or Azure CLI command to assign OAuth permissions. Instead we will leverage an authenticated call to the Microsoft Graph to assign the permissions. For more in depth information about Azure AD apps, verifying the results, and more please see the following post which I am borrowing heavily from. I had difficulty finding this information so this post is my attempt to spread the word and also add a few clarifications on the ADAL libraries used.
(Read this first!) Automating the creation of Azure AD Applications by Christer Ljung
http://www.redbaronofazure.com/?p=7197
Problem
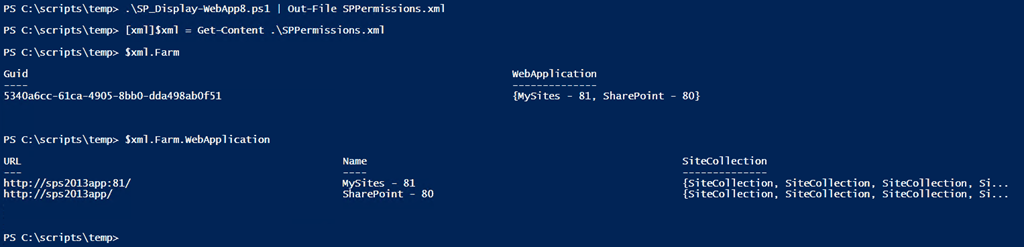
Creating Azure AD apps typically involves logging into the Azure Portal (classic or “new” / Ibiza version) and manually clicking through multiple screens. When developing a solution that needs to leverage Office 365 services (as is my case with a current project) it is helpful to automate the process of creating the Azure AD app and assigning the permissions. If you happen to be assigning Admin permissions then additional steps will be required by an Azure AD domain administrator (see following screenshot).

Solution
Creating an Azure AD application can be accomplished in 2 lines of PowerShell. Login to Azure then create the app.
Login-AzureRmAccount
$aadapp = New-AzureRmADApplication -DisplayName "Some amazing app" -HomePage https://localhost:8081/ -IdentifierUris https://localhost:8081/
***BONUS***
If you want to create an app that uses certificate based authentication you can use the following PowerShell commandlets.
Note: The commandlets for creating and exporting a certificate require Windows 8 or higher. There are workarounds for Windows 7 or similar OS. Feel free to reach out if you are in that scenario.
$pwd = Read-Host -AsSecureString -Prompt "Enter certificate password"
# process for Windows 8+ type OS
$ssc = New-SelfSignedCertificate -CertStoreLocation cert:\localmachine\my -Provider "Microsoft Enhanced RSA and AES Cryptographic Provider" `
-Subject "cn=MySuperSpecialCert" -KeyDescription "Used to access Azure Resources" `
-NotBefore (Get-Date).AddDays(-1) -NotAfter (Get-Date).AddYears(1)
# Export cert to PFX - uploaded to Azure App Service
Export-PfxCertificate -cert cert:\localMachine\my\$($ssc.Thumbprint) -FilePath ExportedSpecialCertFile.pfx -Password $pwd –Force
$KeyStorageFlags = [System.Security.Cryptography.X509Certificates.X509KeyStorageFlags]::Exportable, [System.Security.Cryptography.X509Certificates.X509KeyStorageFlags]::MachineKeySet, [System.Security.Cryptography.X509Certificates.X509KeyStorageFlags]::PersistKeySet
$certFile = Get-ChildItem –Path <path to certificate file>
$x509 = New-Object System.Security.Cryptography.X509Certificates.X509Certificate2
$x509.Import($certFile.FullName, $pwd, $KeyStorageFlags)
$certValue = [System.Convert]::ToBase64String($x509.GetRawCertData())
# should match our certificate entries above.
$validFrom = [System.DateTime]::Now.AddDays(-1)
$validTo = [System.DateTime]::Now.AddYears(1)
$aadapp = New-AzureRmADApplication –DisplayName "Some amazing app" -HomePage "https://localhost:8080/" `
-IdentifierUris "https://localhost:8080/" -CertValue $certValue `
-StartDate $validFrom -EndDate $validTo
The next step involves granting OAuth permissions to the recently created Azure AD app. As of the writing of this blog (Feb 2, 2018) there is not a PowerShell commandlet nor Azure CLI command to assign those permissions. There is however a way to use the Microsoft Graph to assign permissions. This is an adapted version of Christer’s example that I referenced earlier and uses a local version of the Active Directory Authentication Library (ADAL) DLLs. Currently these are at version 3.19.1.
ADAL NuGet package
https://www.nuget.org/packages/Microsoft.IdentityModel.Clients.ActiveDirectory/
Extract the following DLLs into the folder where you are executing other PowerShell commands:
- Microsoft.IdentityModel.Clients.ActiveDirectory.dll
- Microsoft.IdentityModel.Clients.ActiveDirectory.Platform.dll
$Tenant = "<Office 365 tenant name, ex. Contoso>"
$aadTenant = "$Tenant.onmicrosoft.com"
$adminUser = "<admin account with access to authenticate against MS Graph>"
# load ADAL DLLs
$adal = ".\Microsoft.IdentityModel.Clients.ActiveDirectory.dll"
$adalforms = ".\Microsoft.IdentityModel.Clients.ActiveDirectory.Platform.dll"
[System.Reflection.Assembly]::LoadFrom($adal) | Out-Null
[System.Reflection.Assembly]::LoadFrom($adalforms) | Out-Null
$clientId = "1950a258-227b-4e31-a9cf-717495945fc2" # Set well-known client ID for AzurePowerShell
$redirectUri = "urn:ietf:wg:oauth:2.0:oob" # Set redirect URI for Azure PowerShell
$resourceAppIdURI = "https://graph.windows.net/" # resource we want to use
$adminUserId = New-Object "Microsoft.IdentityModel.Clients.ActiveDirectory.UserIdentifier" -ArgumentList ($adminUser, "OptionalDisplayableId")
# Create Authentication Context tied to Azure AD Tenant
$authContext = New-Object "Microsoft.IdentityModel.Clients.ActiveDirectory.AuthenticationContext" -ArgumentList $authority
# Acquire token
$authResult = $authContext.AcquireToken($resourceAppIdURI, $clientId, [Uri]$redirectUri, [Microsoft.IdentityModel.Clients.ActiveDirectory.PromptBehavior]::Always, $adminUserId)
$authHeader = $authResult.CreateAuthorizationHeader()
$headers = @{"Authorization" = $authHeader; "Content-Type"="application/json"}
# make call against MS Graph to apply OAuth permissions
$url = "https://graph.windows.net/$aadTenant/applications/$($aadapp.ObjectID)?api-version=1.6"
$postData = "{'requiredResourceAccess':[
{'resourceAppId':'00000003-0000-0ff1-ce00-000000000000','resourceAccess':[{'id':'fbcd29d2-fcca-4405-aded-518d457caae4','type':'Role'}]},
{'resourceAppId':'00000002-0000-0000-c000-000000000000','resourceAccess':[{'id':'311a71cc-e848-46a1-bdf8-97ff7156d8e6','type':'Scope'}]}
]}";
$result = Invoke-RestMethod -Uri $url -Method "PATCH" -Headers $headers -Body $postData
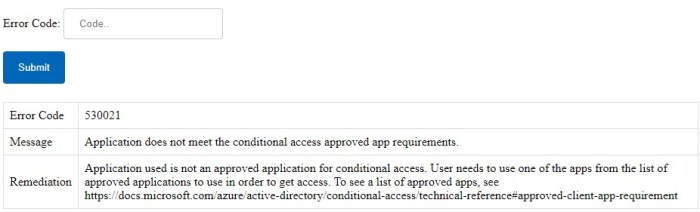
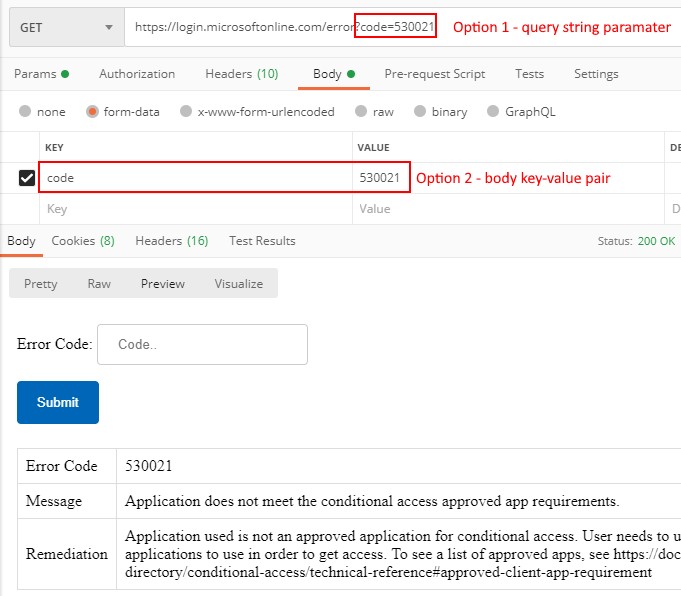
Note the use of specific resoureAppId and resourceAccess values above. These two examples grant the “read and write all items in SharePoint Online” admin consent permission and the default “read user profile data” delegated permission respectively. In order to find out the GUIDs you may need you’ll need to add the permissions through the Azure portal UI, check the manifest file, and extract the GUIDs. See Christer’s post for more details.
<Update 2018-02-06> I recently found out it is possible to list out the Application role permissions and GUIDs needed above by running the following PowerShell against the Azure AD module (I’m using Azure AD “V2” Preview module, haven’t verified against the existing V1 module).
Connect-AzureAD
# 00000003-0000-0ff1-ce00-000000000000 is the AppId for SharePoint Online, call Get-AzureADServicePrincipal by itself to find other AppIds
$SPOApi = Get-AzureADServicePrincipal -Filter "AppId eq '00000003-0000-0ff1-ce00-000000000000'"
$SPOApi.AppRoles
</Update>
If you happen to assign an admin consent permissions (such as the “read and write all items in SharePoint Online” permission) an Azure AD domain administrator will still need to consent to that permission by clicking “Grant permission” inside the Azure portal. I’m not aware of a way to automate that process but if you do know please share in the comments below.
Conclusion
Originally I had hoped automating creation of an Azure AD app would be a simple process. Creation of the Azure AD app is easy, but adding certificate authentication and / or assigning OAuth permissions adds extra work to be done. As seen in this post though much of that can be automated. Hopefully this post saves you time and effort. Feel free to leave any feedback or questions in the comments below.
-Frog Out