This post is a part of Festive Tech Calendar 2022 and a follow-up to Introduction to Calling Microsoft Graph from a C# .Net Core Application from 2018.

Microsoft Graph is the unified API for any developers working with data inside Microsoft 365, Azure Active Directory (Azure AD), Windows, and more. In this post, we’ll cover how to call Microsoft Graph from Polyglot Notebooks (part of .Net Interactive). We’ll also introduce a preview of the Microsoft Graph extension for .Net Interactive.
Background
Do you ever want to test a few lines of code, but have to write dozens of lines of support code (i.e. “boilerplate” or “basic plumbing” code)?
Microsoft Graph has a number of offerings such as quick starts to let you pick a supported code language, download a sample application, and run the project within a few minutes, but this can still take 5-30 mins depending on your level of familiarity.
Separately, there is Microsoft Graph Explorer or the Microsoft Graph Postman collection to quickly execute a query against Microsoft Graph (seconds to minutes usually), but these only execute HTTP REST endpoints and not using SDKs (which I prefer).
I’ve used 3rd party tools such as LINQPad or websites like .Net Fiddle to quickly prototype and execute Microsoft Graph SDK code but these are often disconnected experiences from where I typically develop which is Visual Studio Code.
.Net Interactive and Polyglot Notebooks
Enter .Net Interactive. .Net Interactive builds upon the Jupyter ecosystem (notebooks, kernels, server, etc.) to allow programming in a notebook fashion (executable code alongside text) but with support for multiple languages (C#, F#, JavaScript, PowerShell, SQL, and more). With this added support for multiple languages, the Visual Studio Code extension has been recently renamed to Polyglot Notebooks (previously called .Net Interactive Notebooks), but the base engine itself is still called .Net Interactive.
At a base level, Polyglot Notebooks allow you to write snippets of executable code in multiple languages alongside markdown text blocks. This is great for writing tutorials, sharing a sample of code with someone with explanation (beyond simple comments in the code), or designing a multi-step process of code blocks.
.Net Interactive is also extensible by allowing developers to create custom kernel extensions, magic commands, or script-based extensions.
Microsoft Graph extension for .Net Interactive
During a recent company hackathon event, myself, Jason Johnston, Jon Sequeira, and Diego Colombo built an initial prototype of a Microsoft Graph extension for .Net Interactive. The extension implements a magic command for #!microsoftgraph that can create and authenticate a GraphServiceClient and then binds it to a variable that can then be used in code blocks. The magic command accepts input parameters to control authentication flow, Azure AD application / tenant, Microsoft Graph API version, and more. The current repository includes support for C# (.Net) but we’re also exploring JavaScript and PowerShell in the future.
Prerequisites
There are a few prerequisites that you will need install
- Install the latest Visual Studio Code
- Install the latest .Net 7 SDK (I’m using 7.0.100 at time of publish)
- Install the Polyglot Notebooks extension from the marketplace
Getting started
After above requirements are met, you can get started by following the instructions in the GitHub repo README or the demo notebook.
Let’s take a look at a few samples.
Create a polyglot notebook
To create a new polyglot notebook, open the Command Palette(Ctrl+Shift+P) on Windows or (Cmd+Shift+P) on MacOS, and select Polyglot Notebook: Create new blank notebook. You can also create a new notebook with Ctrl+Shift+Alt+N key combination on Windows.
Build the NuGet package
After forking the repository, navigate to the source directory and run the following command (or execute in a PowerShell code block inside the notebook) to generate a NuGet package which we will then import in the next steps.
dotnet build ./src/Microsoft.DotNet.Interactive.MicrosoftGraph.csproj
Import the NuGet package
After the NuGet package has been built, run the following commands (be sure to replace <REPLACE_WITH_WORKING_DIRECTORY> with the actual directory location) in a C# script block in the notebook to import the NuGet package.
#i nuget:<REPLACE_WITH_WORKING_DIRECTORY>\src\bin\Debug\ #r "nuget:Microsoft.DotNet.Interactive.MicrosoftGraph,*-*"
Help example
Executing the #!microsoftgraph magic command with -h or –help will display the syntax and parameters available for input. Note that options are available with full name (two dashes “–“) or aliases (one dash “-“).
#!microsoftgraph -h

Create client
The following creates an instance of a GraphServiceClient with variable name “deviceCodeClient” using the device code authentication flow. Be sure to replace the input parameters for “YOUR_TENANT_ID” and “YOUR_CLIENT_ID”.
#!microsoftgraph -t "YOUR_TENANT_ID" -c "YOUR_CLIENT_ID" -a DeviceCode -n deviceCodeClient
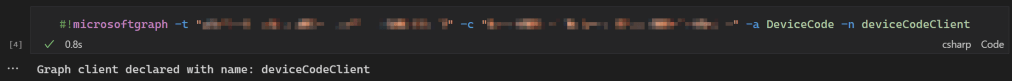
Since we used -n to name the GraphServiceClient instance that is created, we can now use that variable going forward to make requests.
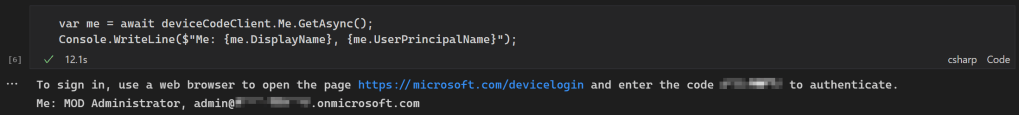
Make requests
Now you can execute Microsoft Graph .Net SDK code using the deviceCodeClient GraphServiceClient just created. We will be prompted to complete the device code authentication flow at this time. Follow the prompt and provide the device code provided.
var me = await deviceCodeClient.Me.GetAsync();
Console.WriteLine($"Me: {me.DisplayName}, {me.UserPrincipalName}");
Live demo
Recently Jason Johnston and I joined the M365 platform community call to give an overview and demo of the Microsoft Graph extension for .Net Interactive. If you want to skip to just the demo, jump to 8:28 timestamp in the video to see things in action.
Conclusion
As you can see, the Microsoft Graph extension for .Net Interactive offers a way to write code and text side by side. There are many scenarios that can benefit from this such as workshop tutorials, exploring the SDKs, prototyping solutions, and more. We welcome your input on feature requests, contributions, raising bugs, etc. Please submit issues or pull requests to the GitHub repository and we will review. Thanks and enjoy!
-Frog Out
Resources
Interactive C# with Polyglot Notebooks (good introduction to getting started with Polyglot Notebooks in .Net Interactive)
https://newdevsguide.com/2022/12/14/polyglot-notebooks-csharp/